Community Certification or simply communism is a joint project by the Telecomix Crypto Munitions Bureau and the PSYCs.
The intention is to distrust the X.509 certification scheme and to provide system wide hooks for web-of-trust or P2P community-driven distribution of certificates or other certificate validation procedures as the ones given by X.509 and hard-coded into most SSL/TLS implementations and web browsers.
Contents |
Why communism?
A lot of things have been called communism lately, like having healthcare. We thought having a community-oriented approach to trusting web sites etc too is communism. Totally. We don't mean this in any way authoritarian – in fact, it's the drastic opposite.
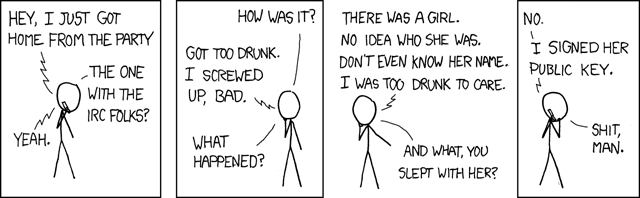
Also you can't beat the nerdy aspect of it:
# apt-get install communism Reading package lists... Done Building dependency tree Reading state information... Done ...
... or just emerge communism
Source
git clone git://git.tgbit.net/libcertpatrol
Battle Plan
Step one to the dancefloor
The goal for the first version of the project is to mimic the behavior of ssh's known_hosts file – to cache public encryption keys in order to make sure they haven't been replaced since last using it, that is – for X.509 certificates on OS-level (the main focus will be on getting it to work with Ubuntu for the first version) rather than application-level (see the excellent Mozilla plugin Certificate Patrol for an example of the latter).
Step two to the dancefloor
In the future it is our aim to come up with an anonymous or pseudonymous and resilient P2P clustering system that allows users to collaborate in a community about detecting changes in a non-compromising way.
This could be done with a simple newscasting approach, but also with something like crypto sharing.
Step three to the dancefloor
Consider ways of providing a system-wide alternative resolution strategy to traditional DNS: Certificates contain keywords
- a user can type in a keyword into the certificate search bar rather than the location or the search engine bar
- one lucky or a series of matches can be presented to the user
- connection is made by mapping the certificate to a known IP address or by other means like DHT
Approach
Patching popular SSL libraries to provide a generic API/interface that allows monitoring applications to add custom certificate/pubkey checking/acceptance/monitoring logic in a unified way to all of the X.509 implementations. A difficult trick (aside from all the masochist code reading & patching which we will not go into detail about here due to our underage attendance) will probably be to present the information in a nice and GUI-y way to the user. Providing a list of "basic" certs with the system could help to fight off the worst amounts of pop-up-spam and system lock-ups :)
See also the discussion on paranoid TLS aka pTLS for background information.
Moving Targets
Listing of aforementioned popular SSL libraries:
- OpenSSL (used by pretty much everything)
- NSS (used by Mozilla & many others)
- GnuTLS
- yaSSL also (not as widely used as the others)
Unintentional Side Effects
See also
- https://cryptoanarchy.org/ (Hash starts with 75:5C:76:B4...)
- http://crypto.telecomix.org
- Pseudonymous multicasting.
- http://www.mail-archive.com/lynx-dev@nongnu.org/msg03566.html